Coming Soon
Coming Soon: Recon-X Platform
Recon-X Platform is being built to help security teams gain earlier visibility into emerging threats — across the clear web, deep web, and dark web — so they can respond faster and reduce risk.
Platform Preview
Coming Soon
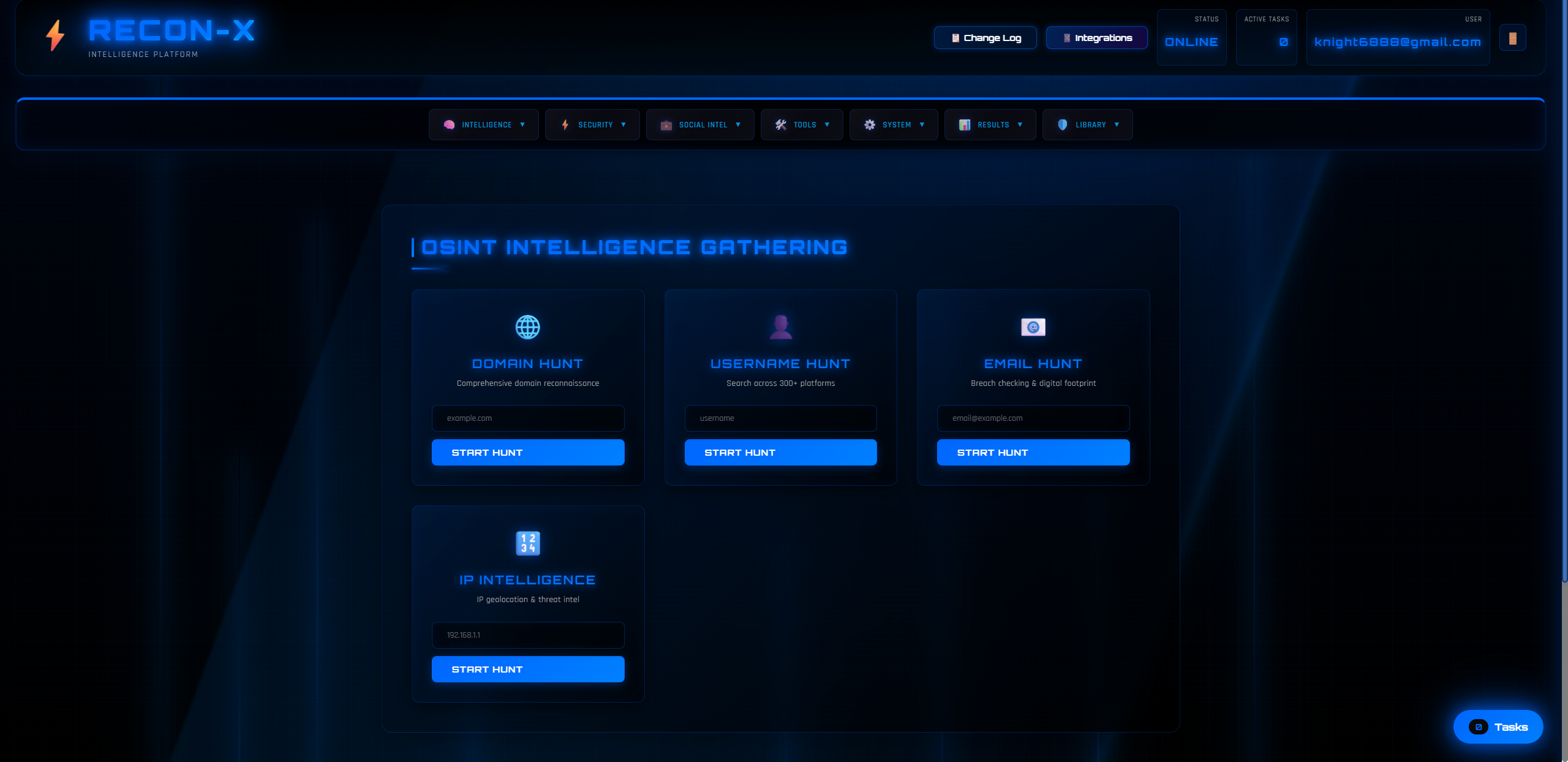
The Recon-X Platform interface is currently in development
Screenshot shows the platform interface in development — features and design may change
The Vision
Security teams today face an overwhelming volume of signals across multiple surfaces. Traditional threat intelligence platforms often focus on known IOCs and historical patterns, leaving gaps in early-stage threat detection. Recon-X Platform is designed to bridge these gaps by providing comprehensive visibility across the entire threat landscape — from public-facing infrastructure to underground forums.
Our platform aggregates intelligence from diverse sources, applies AI-driven enrichment to provide context, and surfaces actionable insights that help teams prioritize and respond more effectively. By monitoring domains, tracking threat actors, detecting credential leaks, and analyzing underground conversations, Recon-X Platform supports proactive defense strategies and faster threat response.
The objective is to deliver actionable data, not just text — intelligence that can be plugged into detections, playbooks, and investigations without heavy manual rework.
The goal is not to replace existing security tools, but to augment them with intelligence that helps teams see threats earlier, understand context better, and make more informed decisions under pressure.
Core Capabilities
Domain & Brand Hunting
Monitor domains, look-alikes, and infrastructure signals linked to threats targeting your organization.
Threat Actor & User Discovery
Track relevant identities and activity patterns to support investigations and proactive defense.
Data Leak & Credential Exposure Monitoring
Identify exposed data and leaked credentials so you can act quickly.
Telegram & Underground Mentions
Detect conversations and mentions that may indicate intent, targeting, or ongoing campaigns.
IOC Engines + AI Enrichment
Aggregate IOCs and enrich them with context to support triage, hunting, and response workflows.
Domain & Brand Hunting
Organizations face constant threats from domain squatting, typosquatting, and look-alike domains designed to deceive users or host malicious infrastructure. Recon-X Platform continuously monitors domain registrations, DNS changes, and certificate issuances to identify potential threats targeting your brand or infrastructure.
The platform tracks domains that closely resemble your legitimate domains, monitors subdomain takeovers, and identifies infrastructure patterns that may indicate reconnaissance or preparation for attacks. By correlating domain data with threat intelligence feeds and historical patterns, the platform helps you prioritize which domains require immediate action.
Integration with certificate transparency logs, passive DNS databases, and threat intelligence feeds ensures comprehensive coverage. Alerts can be configured based on domain similarity scores, registration patterns, and associations with known threat actors or infrastructure.
Threat Actor & User Discovery
Understanding who is targeting your organization — and how — is critical for effective defense. Recon-X Platform tracks threat actors, their aliases, activity patterns, and associations across multiple platforms and underground communities.
The platform maintains profiles of threat actors, including their known aliases, preferred attack techniques, target industries, and historical activity. By monitoring their communications, tool releases, and infrastructure changes, the platform helps you anticipate potential targeting and adjust your defenses accordingly.
User discovery capabilities extend beyond known threat actors to include individuals who may be discussing your organization, planning attacks, or sharing information that could be used against you. The platform tracks mentions, associations, and activity patterns to help you identify emerging threats before they materialize.
All tracking is performed with respect to privacy and legal boundaries, focusing on publicly available information and signals that indicate malicious intent or targeting behavior.
Data Leak & Credential Exposure Monitoring
Credential leaks and data breaches are among the most common initial attack vectors. When credentials are exposed — whether through data breaches, paste sites, or underground markets — attackers can use them to gain unauthorized access to systems and accounts.
Recon-X Platform continuously monitors paste sites, breach databases, underground forums, and credential markets for exposures related to your organization. The platform tracks email addresses, usernames, password hashes, API keys, and other sensitive data that may have been leaked or sold.
When exposures are detected, the platform provides context about the source, the type of data exposed, and when it was first seen. This information helps you prioritize response efforts, determine the scope of potential compromise, and take immediate action to mitigate risk.
Integration with your identity management systems allows for automated credential rotation and account remediation workflows, reducing the time between detection and response.
Telegram & Underground Mentions
Underground forums, Telegram channels, and other private communication platforms are often where threat actors plan attacks, share tools, and discuss targets. Monitoring these channels can provide early warning of potential threats and help you understand attacker motivations and methods.
Recon-X Platform monitors publicly accessible Telegram channels, underground forums, and other communication platforms for mentions of your organization, your industry, or patterns that may indicate targeting. The platform analyzes conversations to identify discussions about potential attacks, tool development, or information gathering activities.
Natural language processing and AI enrichment help distinguish between casual mentions and serious threats, reducing noise and focusing attention on signals that require action. The platform provides context about the source, the nature of the discussion, and any associated threat actors or infrastructure.
All monitoring is performed in compliance with platform terms of service and legal requirements, focusing on publicly available information and signals that indicate malicious intent.
IOC Engines + AI Enrichment
Indicators of Compromise (IOCs) — such as IP addresses, domains, file hashes, and email addresses — are essential for threat detection and hunting. However, raw IOCs without context are often difficult to prioritize and act upon.
Recon-X Platform aggregates IOCs from multiple sources, including threat intelligence feeds, open-source repositories, and platform-generated detections. The platform then enriches these IOCs with context using AI-driven analysis, historical data, and correlation with known threat patterns.
Enrichment includes information about the IOC's origin, associated threat actors, historical usage patterns, and potential impact. The platform also provides confidence scores and recommendations for how to use each IOC in your security operations.
Integration with SIEM systems, EDR platforms, and other security tools allows for automated IOC ingestion and alerting. The platform supports standard IOC formats and can be configured to match your existing workflows and tooling.
AI enrichment helps reduce false positives by providing context that helps analysts distinguish between benign and malicious indicators. The platform learns from your feedback and adjusts enrichment models to better match your organization's risk profile and operational needs.
Use Cases
Proactive Threat Hunting
Use Recon-X Platform to identify emerging threats before they impact your organization. Track threat actors, monitor infrastructure changes, and detect early signals of potential attacks.
Intelligence Services
During an incident, quickly identify related infrastructure, threat actors, and attack patterns. Use enriched IOCs and context to accelerate investigation and containment efforts.
Brand Protection
Monitor for domain squatting, look-alike sites, and unauthorized use of your brand. Detect and respond to brand impersonation attacks before they cause damage.
Credential Compromise Prevention
Detect credential leaks and exposures early, before attackers can use them. Integrate with identity management systems for automated remediation and account protection.
Threat Intelligence Enrichment
Enhance existing threat intelligence with context, correlation, and enrichment from Recon-X Platform. Improve IOC quality and reduce false positives in your security operations.
Security Awareness & Training
Use platform insights to inform security awareness programs and training. Share examples of real threats and attack patterns to help teams understand the threat landscape.
Key Benefits
Architecture & Technology
Recon-X Platform is built on a modern, scalable architecture designed to handle large volumes of data while maintaining low latency and high availability. The platform uses distributed data collection, real-time processing, and AI-driven enrichment to provide timely and actionable intelligence.
Data collection engines continuously monitor multiple sources, including RSS feeds, API endpoints, public databases, and specialized threat intelligence repositories. Data is normalized, deduplicated, and stored in a graph database that enables efficient querying and relationship analysis.
AI enrichment leverages local language models to provide context and classification without sending sensitive data to external services. This approach ensures privacy, reduces latency, and allows for customization to your organization's specific needs.
The platform's API-first design enables integration with existing security tools and workflows. Standard formats and protocols ensure compatibility with SIEM systems, EDR platforms, and orchestration tools.
Security and privacy are built into the platform from the ground up. All data is encrypted in transit and at rest, access is controlled through role-based permissions, and audit logs track all platform activity. The platform complies with relevant privacy regulations and can be deployed on-premises or in private cloud environments if required.
Get Early Access
Recon-X Platform is currently in development. Join our early access program to be among the first to experience the platform and help shape its future.
Recon-X Platform provides intelligence and monitoring insights to support security decision-making. It does not guarantee prevention of all attacks.